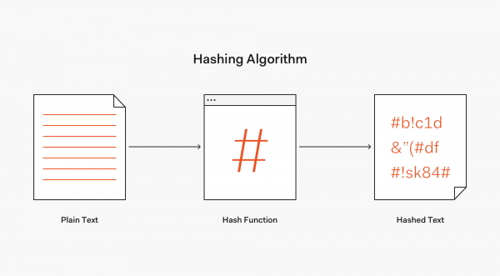
Hashing is the process of transforming a string of characters into a shorter, fixed-length value or key to be stored and recalled at a later date. This process could be looked at like we are "fingerprinting" the data so when we are looking for it in the future, we only need to search for the fingerprint. This is usually faster than searching for the data directly.
Hashing is most often used for the implementation of hash tables. A hash table stores values and keys in a list that is accessible via an index. Because both keys and values are unlimited, the hash function will map the keys to the table size. A hash value is then used as an index.
A function creates a new value according to a hashing algorithm, known as a hash value, or simply a hash. To prevent the conversion of hash back into the original key, a good hash always used a one-way hashing algorithm.
Commonly used Hashing Algorithms
MD5
MD5 is a hashing algorithm that provides a one-way cryptographic function that accepts a message of any length as an input and returns a fixed-length digest value which is used for authenticating the original message.
The MD5 function was made to be used as a secure cryptographic hash algorithm for authenticating digital signatures but has been deprecated for other uses.
Example of an MD5 hash:
Before: This is an example of what an MD5 hash looks like
After: 6ce73c69a99190224dcf239b98a4ddec
SHA-1
SHA-1 (Secure Hash Algorithm 1) was another method of hashing, developed by the U.S. government in the 1990s to become the ultimate algorithmic methodology for encryption. However, this was proven wrong when hackers were able to figure out methods which allowed attackers to spoof content, perform phishing attacks or perform man-in-the-middle attacks.
Example of an SHA-1 hash:
Before: This is an example of what an SHA-1 hash looks like
After: 5e82e644e3427dc4ee25f1cba967b98b40403055
SHA-2
SHA-2 (Secure Hash Algorithm 2) was a successor to the SHA-1 hashing algorithm and it was developed to be more secure. This was a success for the SHA algorithm and this version of the algorithm is widely used today. This Hashing Algorithm was created by the U.S. National Security Agency in 2001.
Example of an SHA-2 hash:
Before: This is an example of what an SHA-2 hash looks like
After: cb057be4100aa4b3d6a53f472e46cbe5bf783f20f3cc740b96967a5a